Blue-Tick Phishing Exploits, LockBit Targets Architecture, Russian Zulip Phishing – Cybersecurity News [August 28, 2023]

Quick Answer
Here’s this week’s phishing newsletter, bringing you the latest updates on . You will find details of cyber threats involving phishing campaigns across diverse fronts in this update, from new targeting X users to Russian threat actors using the Zulip Chat App to carry out diplomatic phishing.
Here’s this week’s phishing newsletter, bringing you the latest updates on
phishing attacks
. You will find details of cyber threats involving phishing campaigns across diverse fronts in this update, from new
phishing scams
** targeting X users** to Russian threat actors using the Zulip Chat App to carry out diplomatic phishing.
****Blue-Tick Phishing Scams Exploit X Customer Complaints
Malicious players online are leveraging the frustration of consumers who seek customer support from various organizations by posting complaints on X (formerly Twitter). Scammers are impersonating different customer support agents, acting through fake X handles to entice unsuspecting victims with refunds.
The new X Premium subscription service now allows anyone to purchase a blue-tick verification badge for a small fee. This rule has substantially led to a compromise in the credibility of these badges.
As the number of malicious actors using the blue tick rises, users must exercise extra caution with new scams. Scammers can manipulate the trust associated with verified accounts and deceive individuals into disclosing sensitive information.
Instances of this scam include fake airline and bank agents targeting people posting complaints. Such incidents highlight the need for extra vigilance to address this emerging threat.
****LockBit Locker Ransomware Targets Spanish Architecture Organizations
Spain’s National Police have warned about an ongoing LockBit Locker ransomware campaign. Instances of
ransomware phishing
are on the rise, and in a new scam, malicious players target architecture organizations with well-crafted phishing emails.
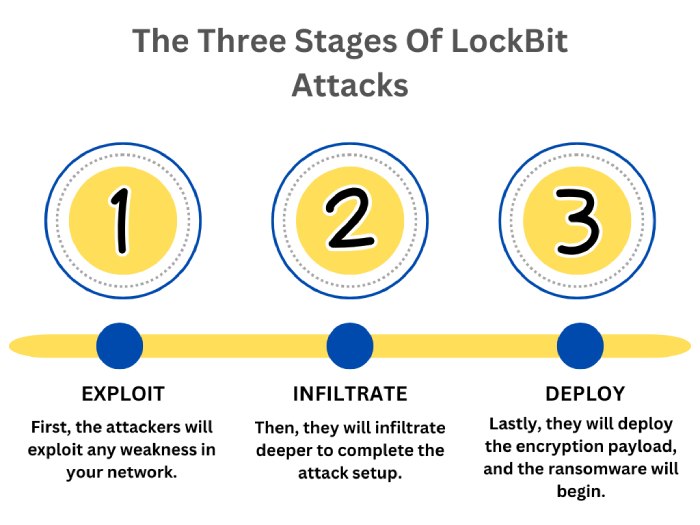
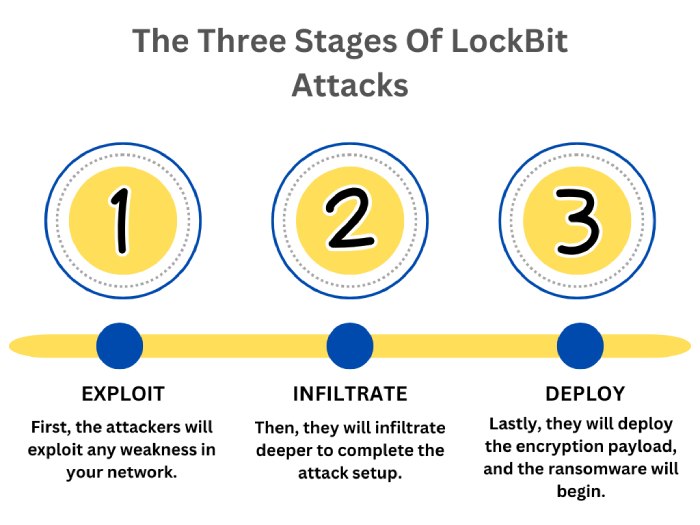
The threat actors operate under the guise of a photography store. After establishing trust with victims by asking for plan drawings and cost estimates for renovating their store, they launch a multi-stage attack . After exchanging a few messages, adversaries eventually send an email with a malicious Python script.
Therefore, organizations in the architecture sector are advised to bolster their vigilance and draw their line of defense against
phishing scams
. To remain secure, experts recommend refraining from opening unexpected email attachments and adopting robust cybersecurity safeguards. Such measures go a long way in reducing the risk of falling victim to such campaigns.
Russian Threat Actors Use Zulip Chat App in Diplomatic Phishing Attacks
A campaign targeting NATO-aligned foreign affairs ministries has revealed the involvement of Russian threat actors. The campaign uses PDF documents diplomatically integrated with Zulip, an open-source chat application. It is capable of exploiting command-and-control operations to deliver malware using legitimate traffic.
Since the attackers use legitimate services to hide their malicious activities, it is highly challenging to detect the threats. The campaign involves the malware APT29 , known for its sophisticated tactics and ability to use legitimate internet services for communication.
Political organizations and governments remain the primary targets of these attackers. The incident underscores the evolving tactics of malicious actors and highlights the pressing need for robust defense mechanisms, including phishing protection, to counter these attacks effectively.
****Google Crypto Ad Scam: Victim Loses $900,000
A victim fell prey to a Google ad scam, which inflicted a staggering loss of $900,000 . As per reports, the victim clicked on a Google ad named “CELER.” It redirected the person to a phishing website that impersonated an authentic cryptocurrency network.

The
phishing scam
drained the victim’s wallet within minutes after a transaction permit was unknowingly signed. The online attackers quickly transferred the stolen funds to different addresses.
The incident highlights the importance of scrutinizing ad links and verifying the authenticity of websites before disclosing sensitive information.
This news about phishing should serve as a wake-up call for industry players, including exchanges. It emphasizes the importance of implementing robust security measures , including phishing awareness training, to effectively combat these scams.
Protect Your Organization
Topics

General Manager
Founder and General Manager of DuoCircle. Product strategy and commercial lead across DuoCircle's 2,000+ customer base.
LinkedIn Profile →Protect your inbox from phishing attacks
Real-time email security with 60-day free trial. No credit card required.