Cloud-Based Strategies For The Prevention Of Phishing Across Your Organization

Quick Answer
Modern phishing scams exploit cloud identity, email, and SaaS expansion at scale. Effective phishing attack prevention must combine technical controls, user-centric defenses, and rigorous governance aligned to regulatory expectations, with strong

Modern phishing scams exploit cloud identity, email, and SaaS expansion at scale. Effective phishing attack prevention must combine technical controls, user-centric defenses, and rigorous governance aligned to regulatory expectations, with strong phishing protection embedded across every layer. For any financial institution, this is not only about cybersecurity; it is also about consumer protection, fraud prevention, and compliance with statutes such as the Bank Secrecy Act.
By unifying telemetry and response across cloud services, you improve risk management, accelerate incident reporting, and help bank customers avoid phishing that could lead to identity theft or account takeover. The following strategy stack shows how to identify phishing scams in real time, harden trust, and orchestrate enforcement actions when needed.
Assess cloud phishing risk and attack surface
Map email, identity, and SaaS exposure
Start with an inventory of email routes, identity providers, and SaaS reliance
. Quantify volumes of phishing emails, email scams, and fraudulent communications reaching users and shared mailboxes. Catalog identities with elevated privileges and third-party OAuth grants. This baseline enables targeted phishing attack prevention and better scam detection across bank operations.

Prioritize VIP targets and third-party integrations
Executives, payment operations, and customer-facing teams face disproportionate security threats. Review vendor integrations , delegated inboxes, and forwarding rules for suspicious activity. Tag VIPs for enhanced
monitoring and security
, and apply just-in-time access controls to limit the blast radius if attackers identify phishing scams that bypass first-line defenses.
Establish metrics that drive risk management
Time to detect and respond to phishing
Percentage of messages with authentication alignment (SPF/DKIM/DMARC)
OAuth app consent risk scores
User propensity to avoid phishing during simulations. These measures tie phishing attack prevention to measurable risk management outcomes in a financial institution.
Harden email and domain trust with cloud-native controls
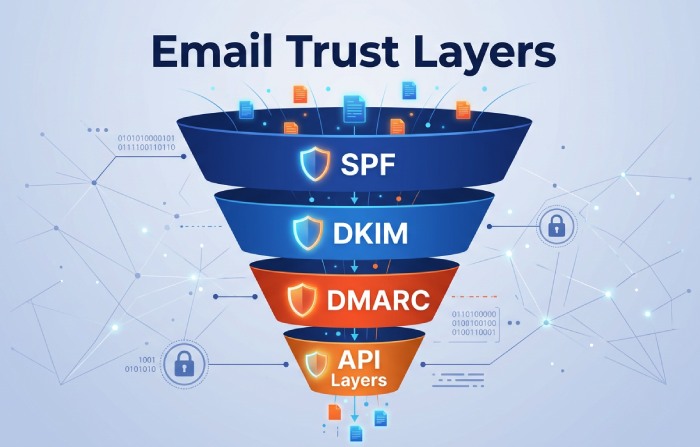
Enforce SPF, DKIM, and DMARC with BIMI
Authenticate every message path. Set DMARC to p=reject with alignment for primary and sending domains; enforce DKIM for bulk mailers ; confirm SPF records for legitimate senders.
BIMI can reinforce brand signals in clients once DMARC is in enforcement, helping users identify phishing scams and avoid phishing sent from look‑alike domains
. These are foundational email security practices that materially cut down phishing scams and phishing emails.
Adopt API-based cloud email security
Layer an API-connected solution alongside native controls for
behavioral analysis
, URL rewriting, and executive impersonation detection. This provides a tool for detection that operates post-delivery and can retract malicious messages across tenants, strengthening online security and digital security without latency penalties. Use this to automate responding to phishing with quarantines, banners, and takedowns.
Monitor brand and look‑alike domains
Launch brand protection to detect typosquats, homoglyphs, and malicious certificate issuance. Integrate domain intelligence with SOAR to trigger enforcement actions such as registrar abuse reports, hoster notifications, and DNS sinkholing. This step protects personal information and supports safe banking by removing infrastructure that hosts phishing scams.
Deploy phishing-resistant authentication and conditional access
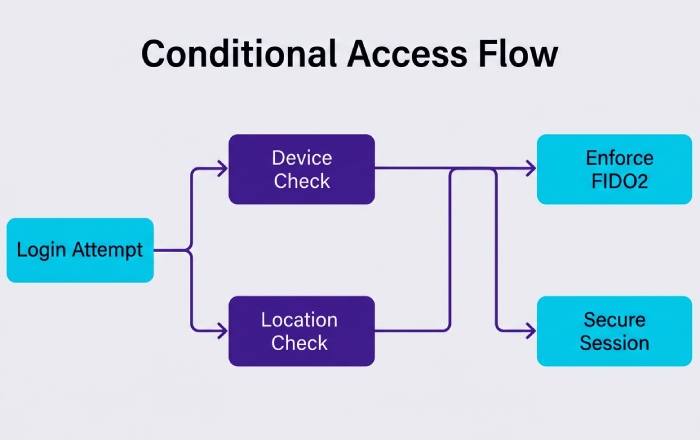
Standardize on FIDO2/WebAuthn for secure login
Phishing-resistant authenticators (security keys and platform biometrics) eliminate OTP relay and push fatigue, dramatically improving account protection. Pair with strong device identity to help users avoid phishing that seeks credentials. This is a cornerstone of cybersecurity and bank security.
Use risk-based MFA, device posture, and continuous access evaluation
Evaluate each session for device health, geovelocity, impossible travel, and token integrity. Conditional Access should elevate to MFA when risk spikes and terminate sessions if device posture degrades. Continuous Access Evaluation catches session theft midstream, bolstering consumer protection and compliance expectations around security incidents.
Apply just-in-time privilege and granular roles
Grant admin rights only when requested and approved, with automatic expiry
.
Limit OAuth scopes
for automation accounts. If you identify phishing scams targeting admins, ephemeral privilege reduces lateral movement, aiding bank management oversight and improving bank operations resilience.
Adaptive policy patterns for responding to phishing
Step-up MFA and re‑verify device compliance after a report of a phishing event
Block legacy protocols that bypass modern email security
Require reauth for sensitive actions after suspicious activity is flagged
Protect SaaS and web sessions with SSE/CASB and isolation
Time-of-click URL protection and sandboxing
Use secure email gateways and API layers to rewrite links and evaluate them at click time. Detonate attachments and URLs in a sandbox before user delivery. DNS/HTTP filtering should block newly registered domains and malware categories, improving consumer compliance posture and reducing security incidents.
Remote browser isolation for untrusted destinations
Send uncategorized or high-risk sites to remote browser isolation. This prevents drive‑by downloads and session token theft while preserving productivity . Isolation significantly raises the cost for attackers running phishing scams and degrades credential-harvesting ROI.
Govern OAuth apps and shadow IT with CASB
Enable OAuth app governance to limit risky third-party consent and revoke stale tokens. CASB data policies can prevent exfiltration of personal information and customer records, supporting account protection and security policies for a financial institution that must meet strict compliance obligations.
Enable cloud-delivered human defense and automated prevention
Adaptive training and realistic phishing simulations
Deliver role-based training aligned to evolving lures (payments, HR, vendors).
Use just-in-time microlearning when users interact with simulated email scams
. Coaching that helps employees
identify phishing scams
teaches them how to avoid phishing in live scenarios, elevating enterprise security awareness.
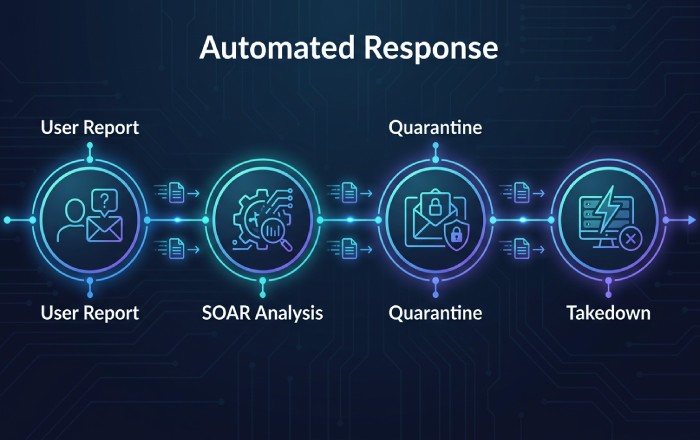
In-line warning banners and report‑phish add‑ins
Insert context-aware banners on external, suspicious, or newly registered domains. Provide a one‑click “report phishing” add‑in integrated with SOAR, enabling rapid incident reporting and triage. These features not only improve scam detection but also create high-fidelity telemetry for fraud prevention and enforcement actions when necessary.
SOAR automation, takedowns, and cross-cloud remediation
Automate message pulls, URL blocking, identity disablement , and domain takedowns. Correlate user reports with threat intel to drive enforcement actions across mail, identity, and endpoints. Integrate with your SAR Program workflow for suspicious activity that implicates funds movement, reinforcing Bank Secrecy Act requirements and organizational risk management.
Align with OCC guidance and banking compliance
Anchor controls to the Bank Secrecy Act and OCC expectations
For banks, phishing attack prevention supports the Bank Secrecy Act mandate to detect and report suspicious activity tied to fraud and financial crime. Map controls to SAR Program processes, ensure timely incident reporting, and document workflows in line with the Comptroller’s Handbook and Third-Party Relationships Guidance. This supports consumer protection and demonstrates mature risk management at a financial institution.
Leverage OCC fraud resources and regulatory tools
Use OCC fraud resources to benchmark policies and enforcement actions trends:
Office of the Comptroller of the Currency (OCC) portals, including BankNet and the Financial Institution Lists
Consumer Protection pages and HelpWithMyBank.gov to guide bank customers on how to avoid phishing and protect personal information
Enforcement Action Search for visibility into enforcement actions themes and remediation patterns
-
_ Comptroller’s Licensing Manual, Licensing Office Contacts, and CAS (Corporate Applications Search) for organizational changes impacting security policies and bank security controls
-
Community Reinvestment Act materials to align customer outreach and safe banking education
Dodd-Frank Act Stress Test insights to integrate cyber operational risk into broader risk management
Digital Media Library, Public Comments, OCC Outreach, and Media Representatives resources for consistent external communications
Comptroller, Annual Report, OCC Alumni, and Bankers and Bank Directors resources for governance context and board engagement on
cybersecurity and consumer compliance
Embed governance across bank management and operations
Establish a risk committee that ties phishing attack prevention to bank management objectives, bank operations continuity , and security policies. Ensure email security, secure login standards, and digital security baselines are audited for compliance. Provide security tips to staff and customers on how to identify phishing scams, avoid phishing, and report phishing. Incorporate online security messages into statements and portals to reduce identity theft risk and reinforce safe banking behaviors.
Practical checkpoints for a financial institution
Maintain a living playbook for responding to phishing, including escalation to legal and regulators when customer harm is likely
Test data flows to confirm account protection and privacy for personal information during investigations
Validate that tools - SSE, CASB, SOAR - integrate as a coherent tool for detection and response, reducing mean time to contain security threats
By aligning cloud-native controls with OCC guidance, the Bank Secrecy Act, and robust fraud resources, institutions strengthen consumer protection , streamline enforcement actions when appropriate, and elevate enterprise-wide risk management against phishing scams.
Topics

General Manager
Founder and General Manager of DuoCircle. Product strategy and commercial lead across DuoCircle's 2,000+ customer base.
LinkedIn Profile →Protect your inbox from phishing attacks
Real-time email security with 60-day free trial. No credit card required.